-


ONEKEY
Vehicle Networking and IoT Product Firmware Security Scanning and Compliance Management Tool
ONEKEY originated in Germany in 2020. Based on its cutting-edge 'binary analysis' technology, it provides users with a centralized solution for the security of connected product firmware, including SBOM management, known vulnerability detection and prioritization, zero-day vulnerability discovery, regulatory compliance, and product lifecycle monitoring, covering your entire SDLC. ONEKEY is committed to becoming the preferred solution for connected product cybersecurity, helping you build secure products, comply with industry standards, resist attacks, and repeatedly execute processes through automation.
ONEKEY supports compliance analysis for more than a dozen international cybersecurity standards, assisting users in quickly meeting the compliance requirements of highly regulated industries, including UN R155, the EU Cyber Resilience Act (CRA), and IEC 62443, and is actively promoting support for the implementation of the national standard GB 44495. ONEKEY is now widely used in areas such as automotive cybersecurity, industrial IoT, and medical devices, and has been highly recognized by typical users including ETAS, Volkswagen, Rolls-Royce, Vodafone, TUV, and Bureau Veritas.

Core values
-
Provide complete visibility of cybersecurity for connected products
-
Ensure the security of OEM self-developed systems and the supply chain
-
Quickly meet the cybersecurity regulatory compliance requirements for products in highly regulated industries
-
Comprehensively manage product security vulnerabilities to reduce cybersecurity risks
-
Improve the efficiency of security vulnerability detection, patching, and reporting, and accelerate product release
-
Continuously monitor product cybersecurity to ensure security throughout the entire lifecycle
-
Avoid legal risks caused by copyright and license issues of open-source software
-
Automated methods simplify manual processes and safety inspection work
Main Benefits
-
ONEKEY provides industry-leading binary analysis technology
-
Extensive support for parsing various embedded product firmware file formats
-
ONEKEY graphical perspective display of the recognition scope for each binary file
-
Provide accurate SBOM and vulnerability analysis results
-
Supports importing, merging, and exporting SBOMs in various standard formats
-
ONEKEY supports automatic scoring and classification based on the risk and relevance of vulnerabilities
-
Provides various vulnerability screening, prioritization, and false positive filtering functions
-
ONEKEY supports automated impact assessment analysis of vulnerabilities
-
Integrates various high-regulation industry laws and standards, easily meeting compliance requirements
-
The interactive Compliance Wizard™ feature supports on-demand generation of compliance reports
-
ONEKEY supports deep analysis of zero-day threats in firmware
-
Zero-day vulnerability reports provide complete context and operational recommendations
-
ONEKEY supports flexible customization of analysis configurations and strategies
-
Continuously monitor firmware security and provide alerts for critical changes
-
ONEKEY extensively supports integration with commonly used CI/CD and third-party management systems
-
The interface is intuitive, the operation is simple, and it is highly user-friendly.
Main Function
-
SBOM Management
-
Known Vulnerability Management
-
Impact Assessment
-
Compliance Management
-
Zero-day vulnerability detection
-
Continuous monitoring
-
Open Source License Analysis
-
Custom Analysis Configuration
-
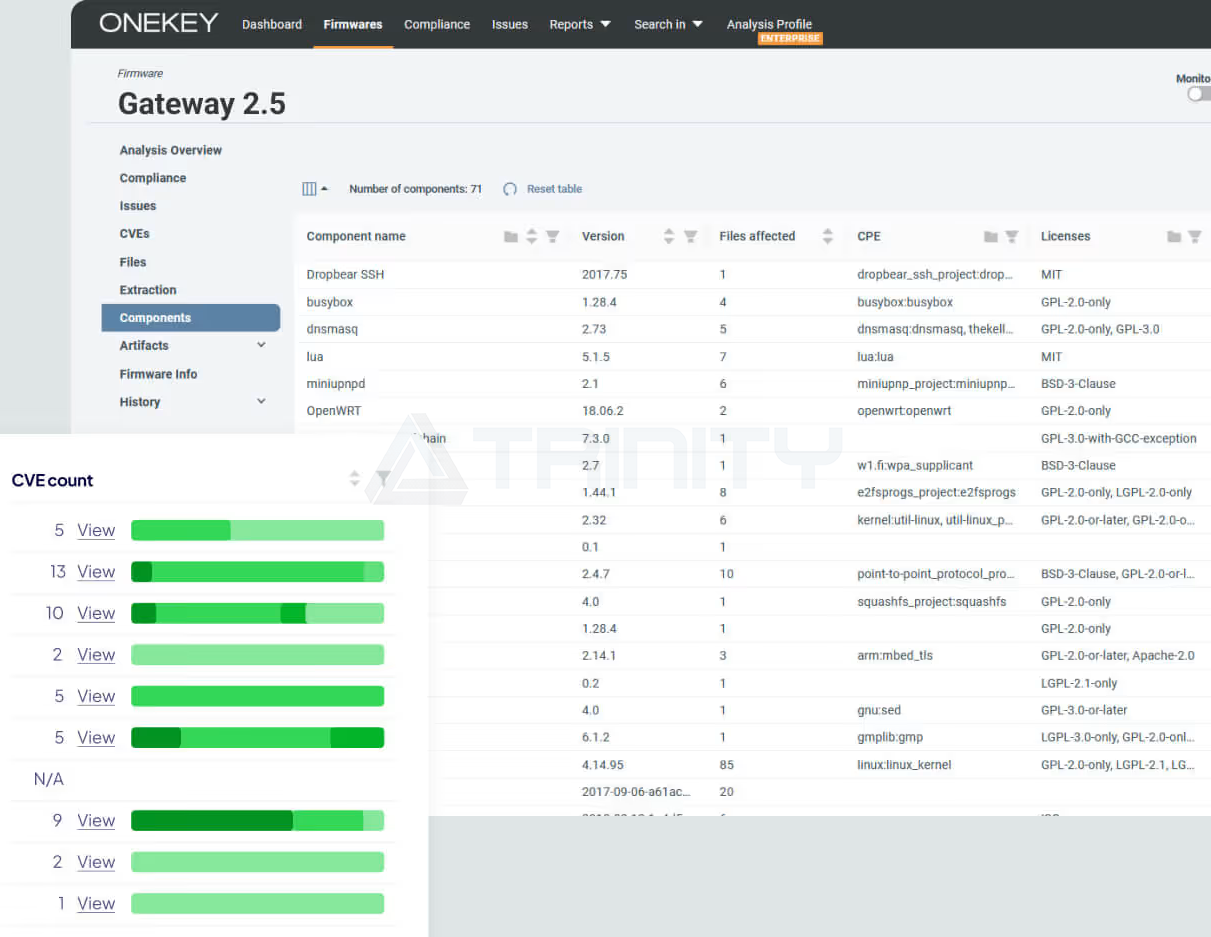
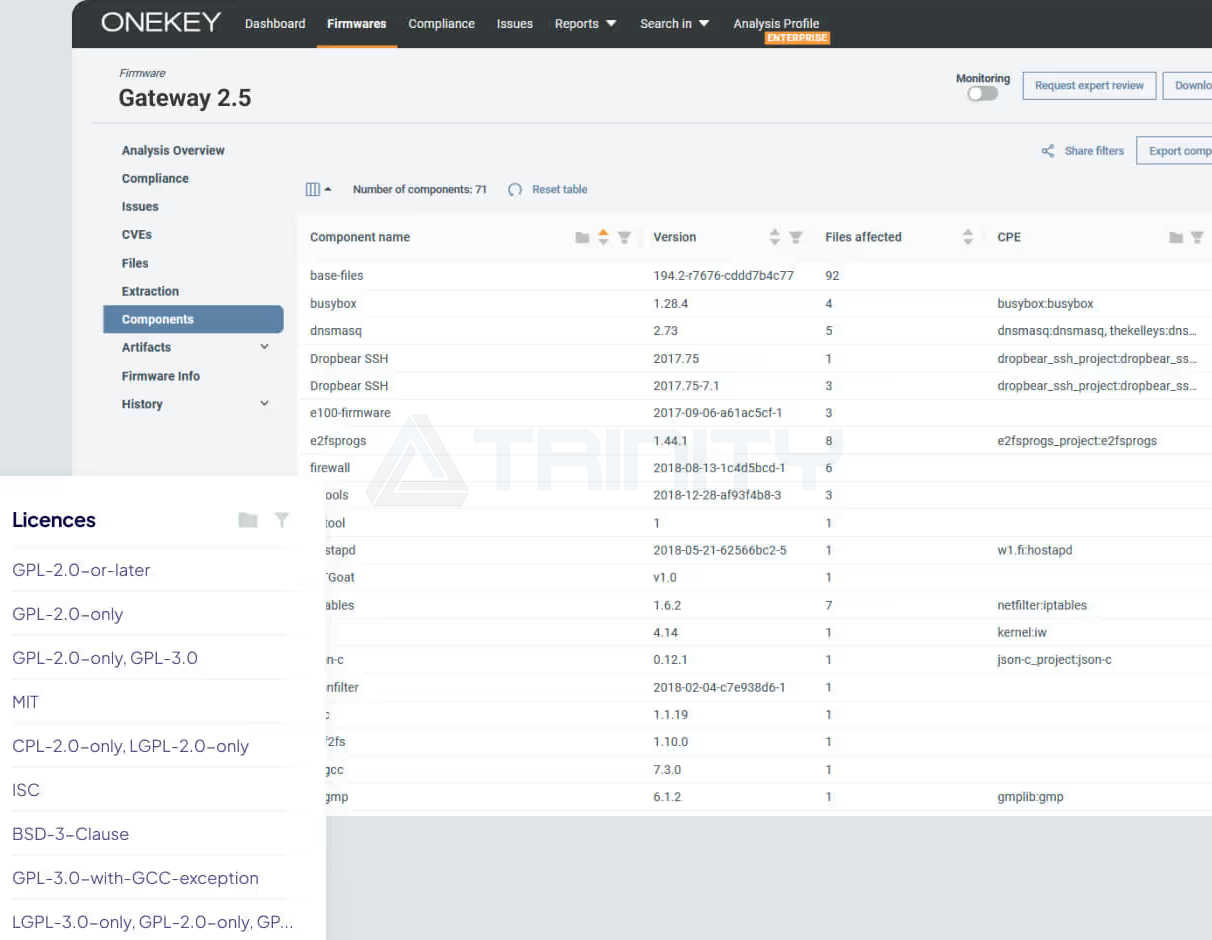
 SBOM Management
SBOM Management Automatically protect your software supply chain. ONEKEY easily generates, imports, and monitors SBOMs, and can export reports in standard formats like CycloneDX and SPDX in just seconds. You can obtain a complete list of components from binary images, source code scanners, or by importing or merging third-party information. You can also upload SBOMs that do not contain the related source code and binary files. The ONEKEY platform continuously and automatically monitors for new unknown or known vulnerabilities.
● Identifying Components from Binary Files
No source code? No problem. ONEKEY generates a comprehensive SBOM directly from compiled binary files. Easily identify components, versions, and license information, providing a reliable foundation for vulnerability management without the need for source code. With ONEKEY's component dependency analysis feature, you can understand how applications and libraries are connected within the firmware, allowing you to trace vulnerabilities across dependency chains, assess their impact on critical components, and understand how updates affect the entire system. All of these features provide you with fully transparent and reliable firmware security detection and management capabilities.
● Complete SBOM
Merged and enhanced for comprehensive coverage. ONEKEY integrates SBOMs from various sources, including manually created files, source code scanners, and third-party data. The ONEKEY platform merges these inputs to create a single, complete SBOM containing VEX and VDR information, providing you with complete and accurate information on software components and related vulnerabilities.
● Advanced Version Detection
High confidence in component matching. Using ONEKEY's proprietary binary analysis method, accurately detect and match component versions. This ensures that you have high confidence in SBOM data, enabling precise CVE matching and proactive vulnerability management.
-
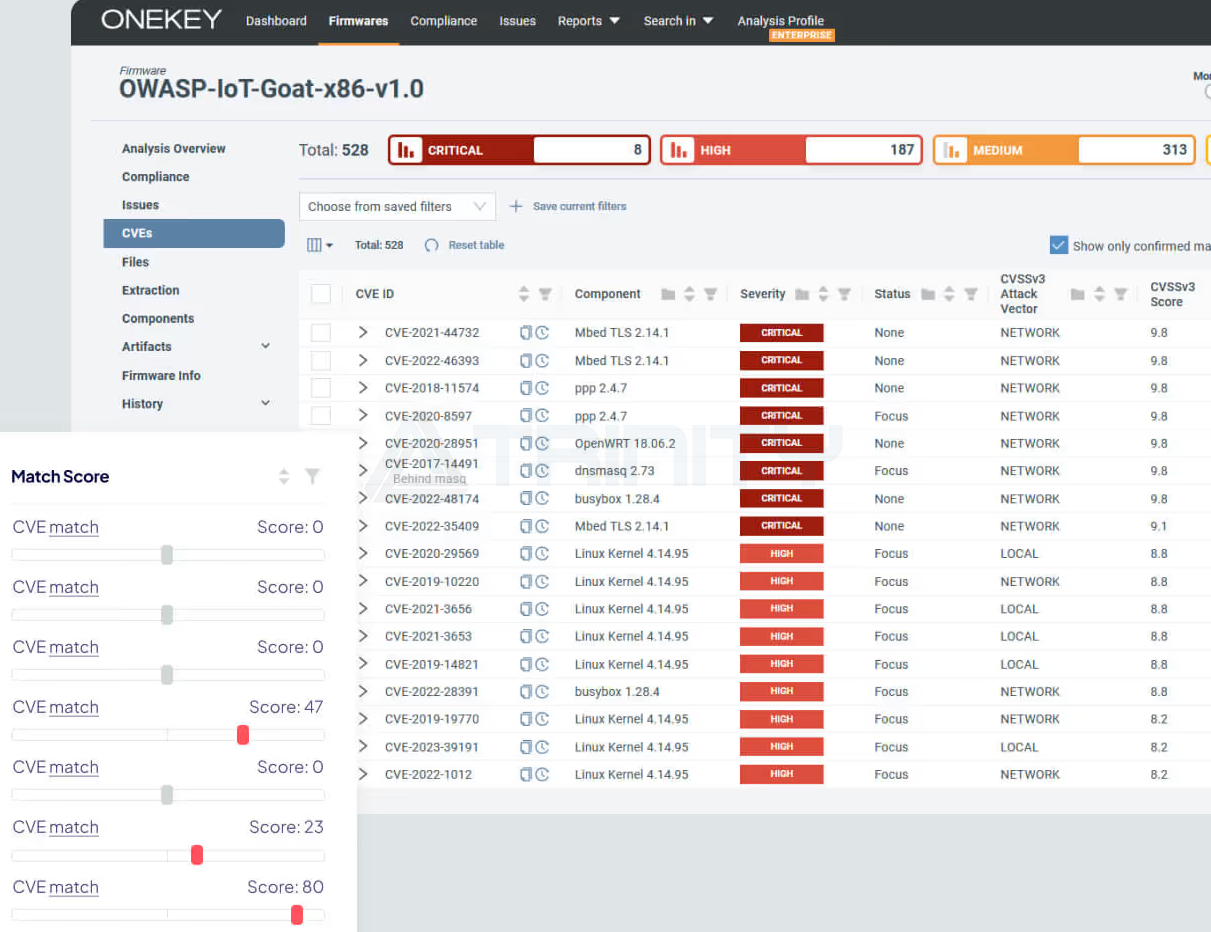
 Known Vulnerability Management
Known Vulnerability Management Complete visibility and prioritized handling of known vulnerabilities (CVEs). Analyzing and managing product security vulnerabilities is not that complicated. With ONEKEY's vulnerability management features, you can seamlessly move from detecting issues to resolving them, always maintaining evidence and confidence, and providing consistent and auditable results. The ONEKEY platform not only recommends the priority of vulnerabilities but also highlights the ones that truly matter in your deployment environment. Integrated risk assessment features (such as CVSS environmental scoring, stakeholder-specific vulnerability classification (SSVC), and transparent VEX data) provide you with a clear understanding of vulnerabilities and support user-defined policies to reduce false positives.
● Proactive Protection
Automatic detection and analysis. The ONEKEY platform continuously scans your firmware for new vulnerabilities and provides detailed reports containing VEX data. By regularly performing automated assessments, it proactively protects your assets and maintains a strong security posture.
● Targeted Fixes
Prioritize addressing the most severe vulnerabilities. Focus your efforts on the most important issues. The ONEKEY platform can eliminate false positives, allowing you to take action on vulnerabilities that may pose real risks in your deployment environment. With the Common Vulnerability Scoring System (CVSS) environmental scores and Stakeholder-Specific Vulnerability Classification (SSVC), you can handle vulnerabilities according to the truly urgent business priorities.
● Improve Efficiency
Reduce response time and effort. ONEKEY provides automated vulnerability classification, risk scoring, argumentation, and decision documentation, thereby eliminating false positives and saving valuable investigation time and resources. With a centralized dashboard, comprehensive SBOM, and audit-ready workflows, security teams can be freed from tedious backlogs, gain a streamlined prioritized view, focus on what truly matters, and turn complex manual processes into fast, repeatable workflows.
-
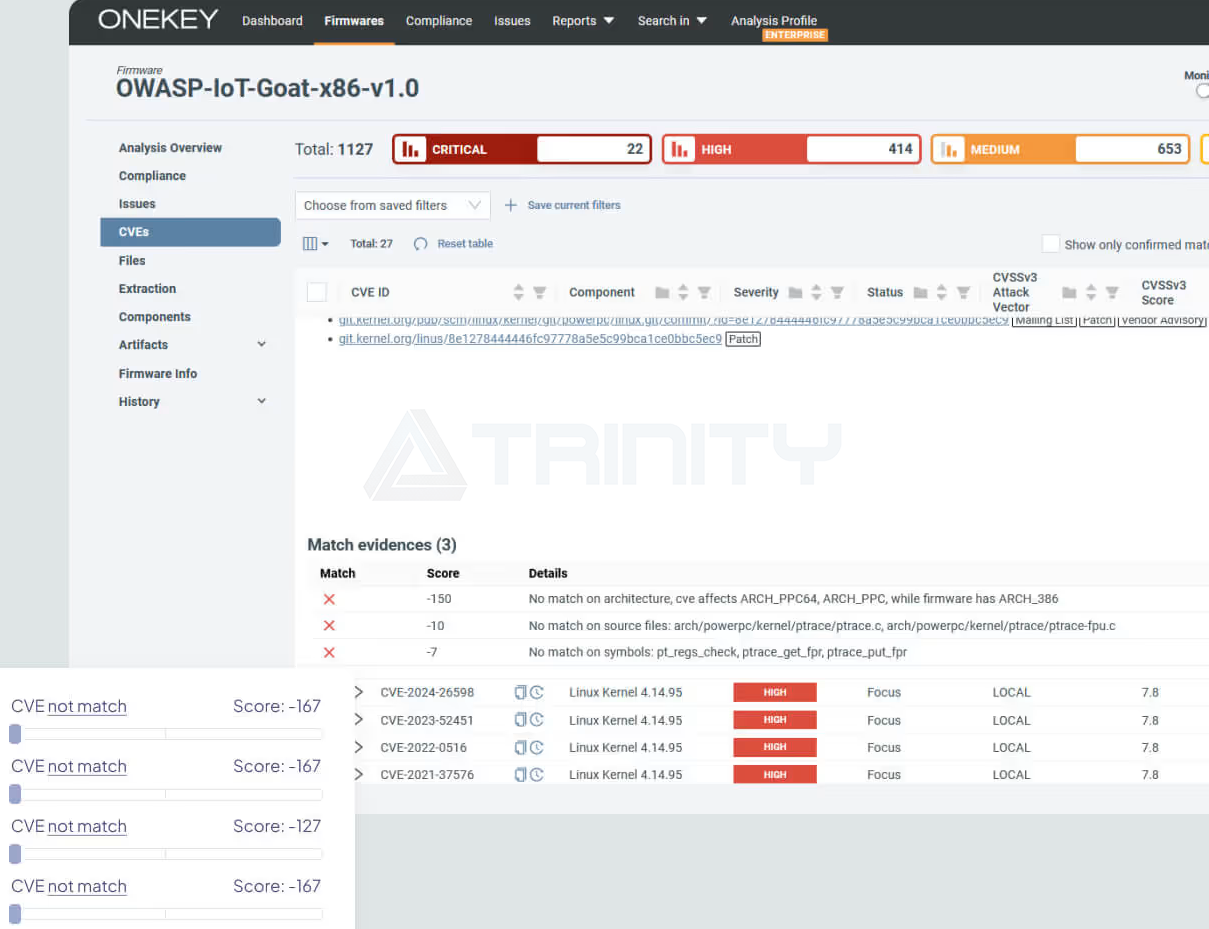
 Impact Assessment
Impact Assessment Focus on relevant vulnerabilities and reduce classification time. ONEKEY analyzes each CVE based on the actual firmware environment and processes thousands of common vulnerabilities (CVEs) within minutes, automatically performing impact assessments to determine whether the vulnerability exists in the firmware and affects your product, enabling your team to focus on truly relevant vulnerabilities. The platform collects evidence and attaches it to existing or deleted CVE matches for your review or record. Through simple and understandable matching scores, you get a completely transparent experience.
● Accurate Scoring
Prioritize handling critical threats. ONEKEY automatic scanning analyzes your firmware based on CVEs according to factors such as component inclusion, binary usage, and symbol matching. Each vulnerability is scored to indicate its relevance to your product. The higher the score, the greater the likelihood that the vulnerability affects the product, allowing you to effectively determine priorities and reduce remediation time.
● Intelligent Filtering
Focus on what matters most. ONEKEY supports one-click filtering of irrelevant CVEs. The "Show Only Confirmed CVE Matches" button highlights critical vulnerabilities while keeping all other accessible vulnerabilities available. This way, you can concentrate on addressing real threats without sacrificing transparency or tracking potential risks.
● Real-time Efficiency
Saves time and resources. Reduces the number of CVEs that need attention by up to 60%. Through ONEKEY's automated classification process, you can save valuable time and resources, allowing your team to focus on resolving critical issues without manual analysis.
-
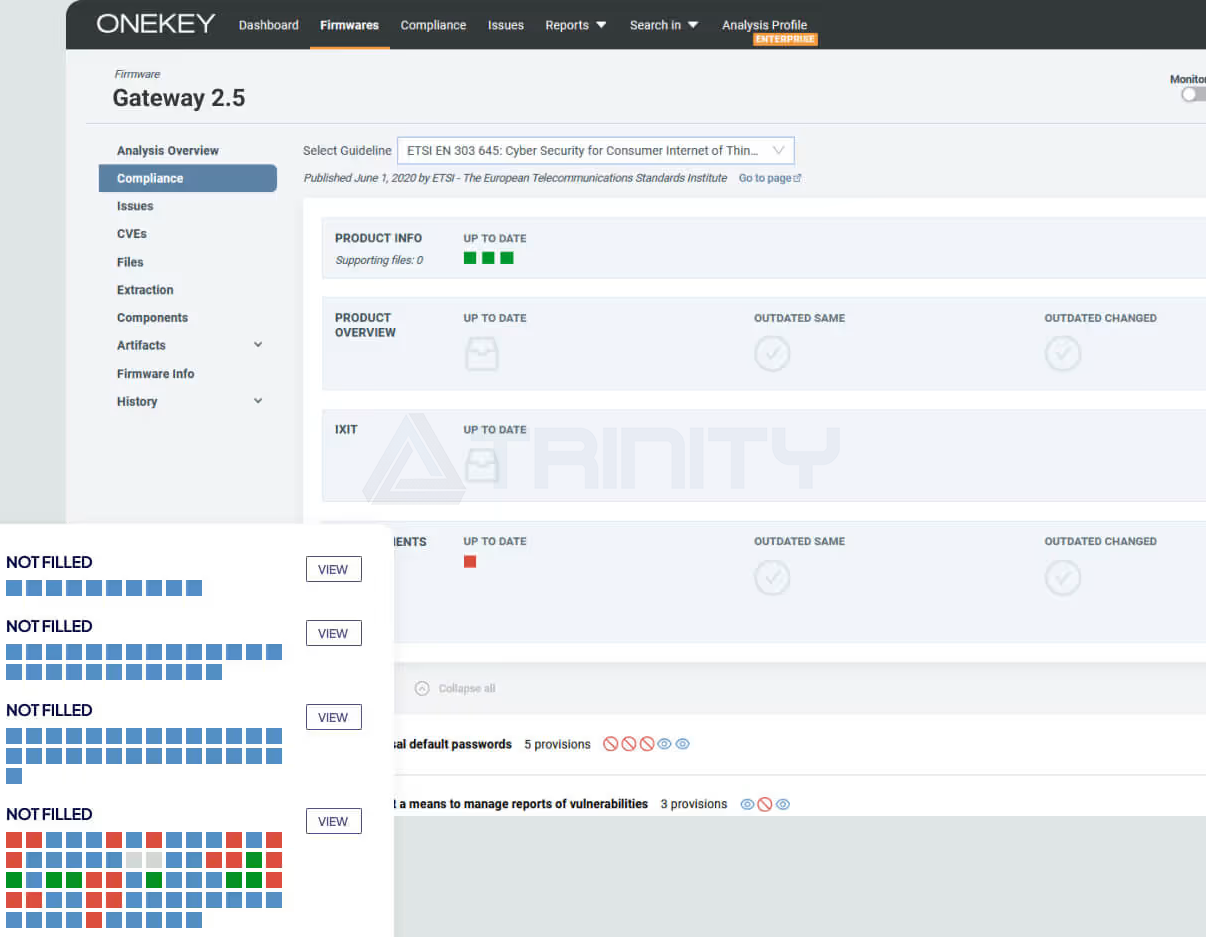
 Compliance Management
Compliance Management Easily achieve compliance. ONEKEY's patent-pending Compliance Wizard™ feature is an interactive regulatory assistant that guides you through complex product cybersecurity assessment processes via conversational compliance analysis and document recording. The editable panel can be customized to your needs for evaluations and automatically extracts uploaded product data. You can also monitor changes, override recommendations, and maintain audit records, simplifying compliance management. Compliance Wizard™ is suitable for standards such as UN R155, the EU Cyber Resilience Act (CRA), RED, IEC 62443-4-2, and ETSI 303 645.
● Integrated Design
A central interface where everything is clear at a glance. ONEKEY Compliance Wizard™ guides you through all technical requirements and compliance self-assessments. An easy-to-understand red-green light system provides clear compliance status and change tracking. Access product information, questionnaires, and requirements through a single dashboard. Gain a comprehensive understanding of ongoing product and regulatory compliance.
● Flexibility
Automated, adjustable documentation. Compliance Wizard™ automatically integrates product data to ensure accuracy and allows for manual tracking or overriding checks as needed. Stay up to date with detailed audit trails and change logs. Easily view regulatory requirements and compliance levels at a glance. Analyze and document technical and organizational compliance in a conversational format. Customize requirements using editable panels and conditional questionnaires.
● Self-Assessment
Generate detailed reports with just one click. Compliance Wizard™ provides a detailed report outlining compliance levels and areas for improvement. Users can export all necessary information in a structured format for self-certification, external certification, and compliance documentation. ONEKEY also supports simplified export of comprehensive compliance packages and the creation of official compliance statements that meet regulations such as CRA. The generated report also includes signature fields.
-
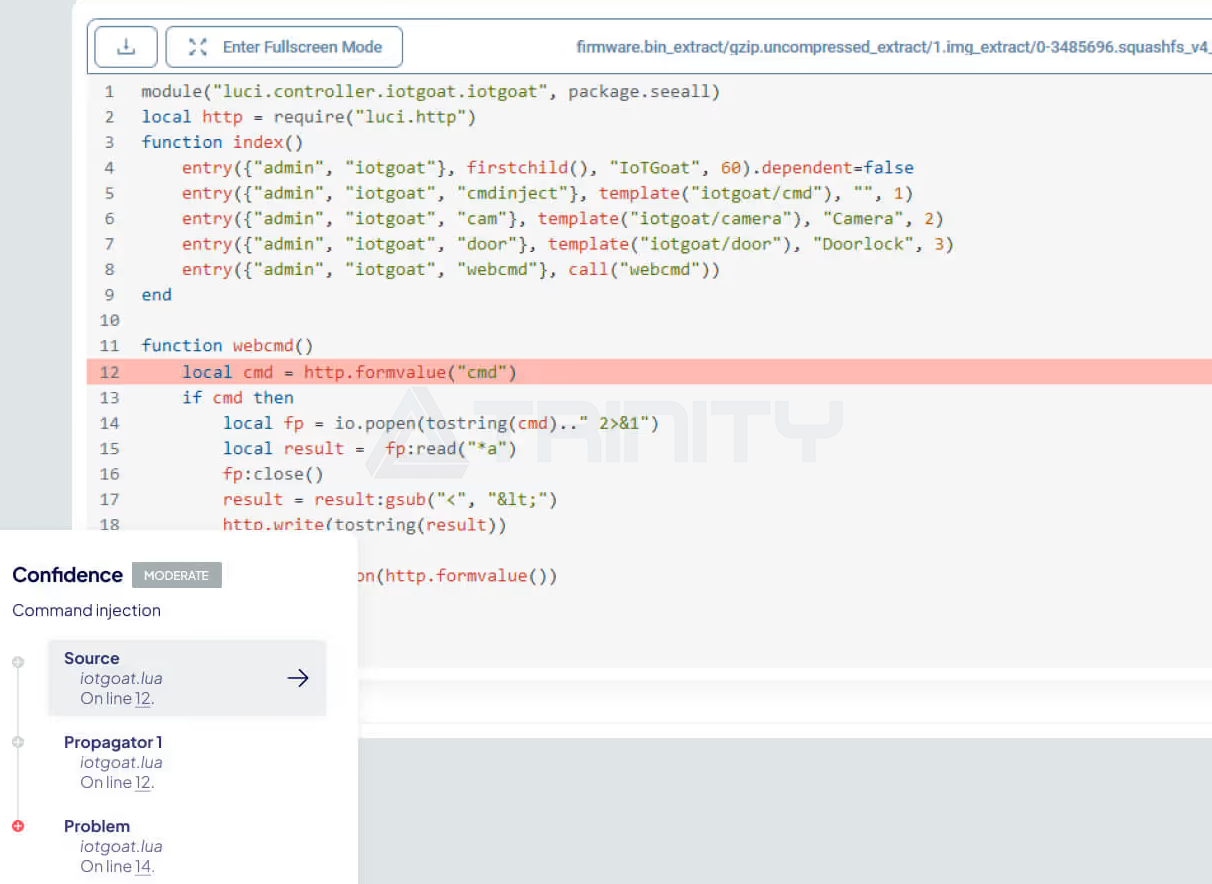
 Zero-day vulnerability detection
Zero-day vulnerability detection Discover hidden threats and avoid security risks early. ONEKEY's zero-day vulnerability detection feature can scan the firmware of your smart devices, industrial control systems, and connected products to find unknown vulnerabilities. Using advanced static analysis techniques, it can accurately pinpoint critical defects that may lead to serious security issues (CWE), such as command injection, insecure communication, or hardcoded credentials. With ONEKEY's zero-day detection feature, you can identify critical risks early, understand their impact, and take action quickly. Receive real-time alerts and clearly understand the issues without extra effort from your team.
● Comprehensive Coverage
Protecting V2X/IoT/OT and other fields. From smart vehicles to industrial systems, ONEKEY's zero-day vulnerability detection covers binaries as well as scripts like PHP, Python, Bash, and Lua. It tracks command injection, buffer overflows, and other critical vulnerabilities in source code and binary code, ensuring nothing is overlooked.
● Act Quickly with Precise Vulnerability Information
Minimize response time, maximize security. Obtain detailed reports on detected zero-day vulnerabilities, including context and recommended actions. Whether it's hidden defects in binary code or script vulnerabilities, ONEKEY provides the information you need to take swift action and ensure system security.
● Deep Static Analysis
Locate and mitigate risks. ONEKEY's advanced static analysis technology can trace data flows within the code, highlighting potential injection points and security vulnerabilities. You can customize detection rules to capture both private and public vulnerabilities. By clearly displaying the entire attack path, you can quickly identify, categorize, and fix vulnerabilities—all of this can be done within a single product module.
-
 Continuous monitoring
Continuous monitoring Continuous monitoring to prevent threats before they occur. Using digital twin technology, ONEKEY performs round-the-clock automatic scans to ensure the security of your firmware. ONEKEY's firmware monitoring system reanalyzes your firmware daily, ensuring continuous security protection throughout its lifecycle. As new vulnerabilities emerge, ONEKEY provides updated analysis results and important alerts through its constantly updated database and enhanced detection capabilities. With continuous firmware monitoring, you can stay one step ahead in defending against threats and maintain transparency, ensuring the security of your firmware in an ever-changing threat landscape.
● Real-Time Alerts
Respond to new threats immediately. Be the first to know when a new vulnerability is discovered. The ONEKEY platform sends real-time alerts about any changes or threats that might affect the security of your product. This ensures that your team can act quickly, minimize exposure time, and protect the security of your product.
● Continuous Scanning
Don't miss security updates. ONEKEY's continuous monitoring feature reanalyzes your firmware daily to ensure your firmware remains secure and maintains a strong security posture when new threats emerge. This continuous scanning feature keeps you always informed of the security status of your firmware without the need for manual intervention.
● Seamless Integration
Simplify your security workflow. ONEKEY's continuous monitoring features perfectly fit into your existing processes and integrate with mainstream CI/CD tools and platforms. Automate your security checks to ensure consistency and security throughout the development process. You can easily track and manage vulnerabilities directly from the dashboard.

-
 Open Source License Analysis
Open Source License Analysis Reduce open source software (OSS) licensing issues and maintain compliance. With ONEKEY's open source license analysis feature, you can easily manage and verify open source licenses. The ONEKEY platform provides a detailed view of all your open source components through advanced SBOM and product data analysis. Automate audits to ensure compliance and prevent potential legal risks. With event record evidence, you can easily respond to lawsuits and maintain accurate records, allowing you to confidently handle the complexities of open source software.
● Automatic Auditing
Easily stay compliant. ONEKEY automatically lists licenses to ensure continuous adherence to open source license requirements. The ONEKEY platform provides automatic reports and tracks any changes to your license status, allowing you to maintain accurate records effortlessly and avoid costly legal issues.
● Real-time Updates
Keep your licenses up to date. ONEKEY's real-time monitoring feature shows any changes to your open source licenses. Stay on top of new requirements and updates to ensure your software is always compliant.
-
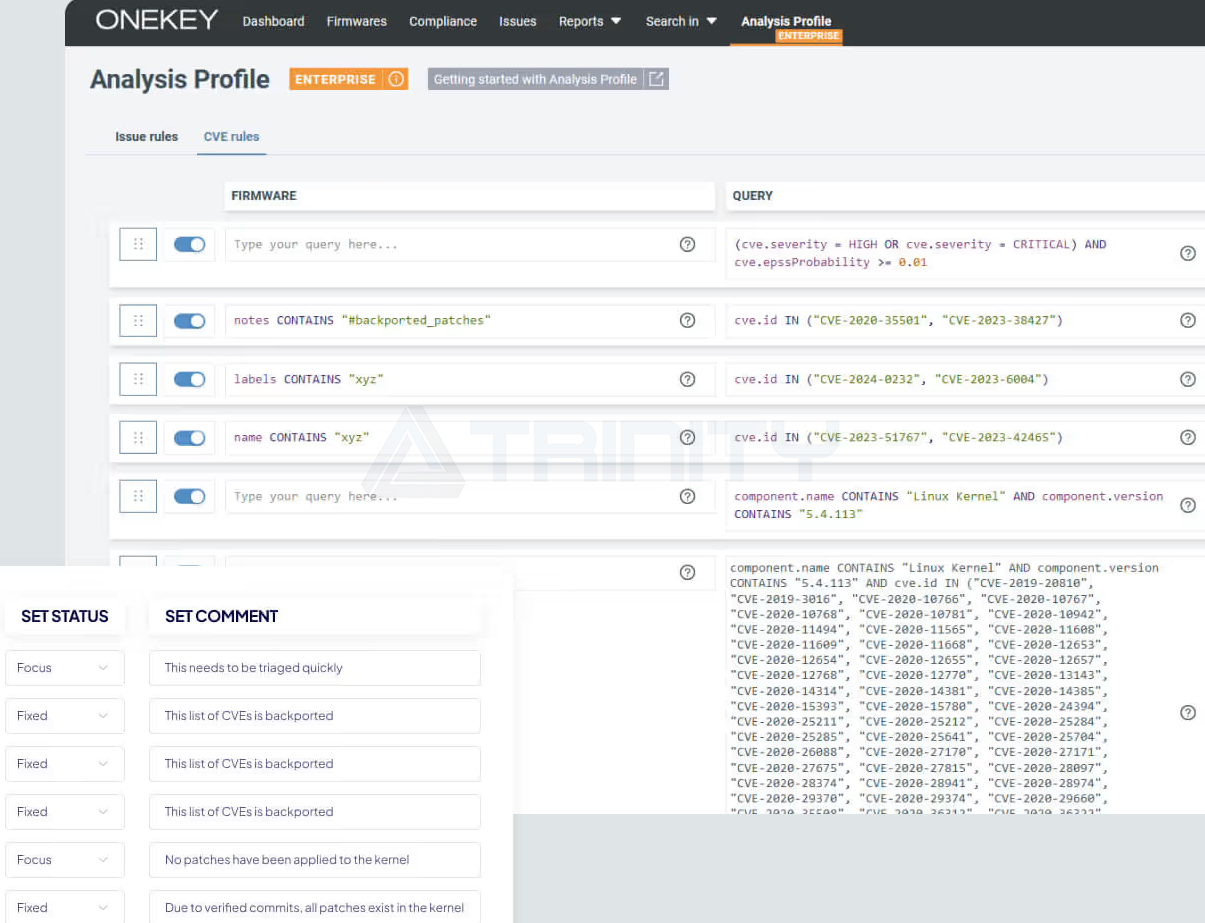
 Custom Analysis Configuration
Custom Analysis Configuration Flexible threat modeling. ONEKEY's proprietary Custom Analysis Profiles™ feature is your preferred tool for tailoring threat modeling and rule integration. You can create personalized threat rules, prioritize CVEs, manage false positives, and define acceptable risk levels for your organization. ONEKEY aligns your analysis with security policies and risk management strategies, ensuring seamless integration with your business needs.
● Flexibility
Automated, customized threat rules. ONEKEY easily integrates product data and automatically assigns detected vulnerability statuses. Use OQL object query language to create detailed rules that reflect your unique security requirements, and track changes through a complete audit trail. View your custom analysis in a dialog format, making it convenient to review and adjust as needed.
● Efficiency
Save time through customized automation processes. ONEKEY supports creating and applying custom rules directly from CVE or zero-day vulnerability pages. With just a few clicks, you can set up automated actions for detected vulnerabilities, reducing manual work and speeding up the classification process, thereby improving work efficiency.
● Control
Manage false positives and risks. Use advanced filtering and rule settings to eliminate distractions and stay focused. Automatically determine the priority of CVEs based on their relevance to your products, or block certain CVEs. This level of control helps you effectively manage false positives and ensures your team can focus on real threats.
Firmware formats supported by ONEKEY
No. | Firmware Format | Processing Type | Is it fully supported? |
1 | 7-ZIP | ARCHIVE | Fully support |
2 | ADVENICA IMAGE | ARCHIVE | Encrypted partitions are not supported |
3 | ALCATEL IMAGE | ARCHIVE | Fully support |
4 | ANDROID AVB | FILESYSTEM | Fully support |
5 | ANDROID BINARY XML FORMAT (AXML) | ARCHIVE | Fully support |
6 | ANDROID BOOTIMG | FILESYSTEM | Fully support |
7 | ANDROID BOOTLOADER (ABL) | ARCHIVE | Fully support |
8 | ANDROID DTBO | FILESYSTEM | Fully support |
9 | ANDROID EROFS | FILESYSTEM | Fully support |
10 | ANDROID OTA | FILESYSTEM | Fully support |
11 | ANDROID SPARSE | FILESYSTEM | Fully support |
12 | ANDROID SPARSE (TRANSFER LIST) | FILESYSTEM | Fully support |
13 | ANDROID SUPER | FILESYSTEM | Fully support |
14 | ANDROID VENDORIMG | ARCHIVE | Fully support |
15 | AR | ARCHIVE | Fully support |
16 | ARC | ARCHIVE | Fully support |
17 | ARJ | ARCHIVE | Fully support |
18 | ARM LINUX KERNEL | EXECUTABLE | Fully support |
19 | AUTEL ECC | ARCHIVE | Fully support |
20 | BELDEN MTS | ARCHIVE | Fully support |
21 | BINARY FLAT (BFLT) | EXECUTABLE | Fully support |
22 | BOSCH CPP | ARCHIVE | Fully support |
23 | BOSCH CPP FILE | ARCHIVE | Fully support |
24 | BTRFS | FILESYSTEM | Fully support |
25 | BZIP2 | COMPRESSION | Fully support |
26 | CAB | ARCHIVE | Fully support |
27 | CISCO ASDM | ARCHIVE | Fully support |
28 | CISCO CBS | ARCHIVE | Fully support |
29 | CISCO SGZ ARCHIVE | ARCHIVE | Fully support |
30 | COMPRESS | COMPRESSION | Fully support |
31 | CPIO (BINARY) | ARCHIVE | Fully support |
32 | CPIO (PORTABLE ASCII CRC) | ARCHIVE | Fully support |
33 | CPIO (PORTABLE ASCII) | ARCHIVE | Fully support |
34 | CPIO (PORTABLE OLD ASCII) | ARCHIVE | Fully support |
35 | CRAMFS | FILESYSTEM | Fully support |
36 | D-LINK ENCRPTED_IMG | ARCHIVE | Fully support |
37 | D-LINK SHRS | ARCHIVE | Fully support |
38 | DAHUA ARCHIVE | ARCHIVE | Fully support |
39 | DAHUA SECRITY | FILESYSTEM | Fully support |
40 | DEVICE TREE BLOB (DTB) | EXECUTABLE | Fully support |
41 | DMG | ARCHIVE | Fully support |
42 | DMVERITY | FILESYSTEM | Fully support |
43 | DOCKER IMAGE | ARCHIVE | Fully support |
44 | ECOS ROMFS | FILESYSTEM | Fully support |
45 | ELF (32-BIT) | EXECUTABLE | Fully support |
46 | ELF (64-BIT) | EXECUTABLE | Fully support |
47 | ENGENIUS | ARCHIVE | Only supports certain versions |
48 | EXTFS | FILESYSTEM | Fully support |
49 | FAT | FILESYSTEM | Fully support |
50 | FESTO FEZLV | FILESYSTEM | Fully support |
51 | FESTO FFWU | ARCHIVE | Fully support |
52 | FREERTOS OTA | ARCHIVE | Fully support |
53 | GZIP | COMPRESSION | Fully support |
54 | GZIP (MULTI-VOLUME) | COMPRESSION | Fully support |
55 | HIRSCHMANN CONTAINER | ARCHIVE | Fully support |
56 | HIRSCHMANN NEWH | ARCHIVE | Fully support |
57 | HP BDL | ARCHIVE | Fully support |
58 | HP IPKG | ARCHIVE | Fully support |
59 | HRFS | FILESYSTEM | Fully support |
60 | INSTAR BNEG | ARCHIVE | Fully support |
61 | INSTAR HD | ARCHIVE | Fully support |
62 | INTEL HEX | EXECUTABLE | Fully support |
63 | ISO 9660 | FILESYSTEM | Fully support |
64 | JFFS2 (NEW) | FILESYSTEM | Fully support |
65 | JFFS2 (OLD) | FILESYSTEM | Fully support |
66 | LITTLEFS | FILESYSTEM | Fully support |
67 | LZ4 | COMPRESSION | Fully support |
68 | LZ4 (LEGACY) | COMPRESSION | Fully support |
69 | LZ4 (SKIPPABLE) | COMPRESSION | Fully support |
70 | LZH | COMPRESSION | Fully support |
71 | LZIP | COMPRESSION | Fully support |
72 | LZMA | COMPRESSION | Fully support |
73 | LZO | COMPRESSION | Fully support |
74 | MASTER BOOT RECORD (MBR) | FILESYSTEM | Fully support |
75 | MEDIATEK MTK | ARCHIVE | Fully support |
76 | MICROCHIP MPFS | FILESYSTEM | Fully support |
77 | MOTOROLA S-RECORD (SREC) | EXECUTABLE | Fully support |
78 | MULTI-SEVENZIP | ARCHIVE | Fully support |
79 | NETGEAR CHK | ARCHIVE | Fully support |
80 | NETGEAR TRX V1 | ARCHIVE | Fully support |
81 | NETGEAR TRX V2 | ARCHIVE | Fully support |
82 | NTFS | FILESYSTEM | Fully support |
83 | PARTCLONE | ARCHIVE | Fully support |
84 | PCK | ARCHIVE | Fully support |
85 | QNAP NAS | ARCHIVE | Fully support |
86 | QNX IMAGE FILESYSTEM (IFS) V4 | FILESYSTEM | Fully support |
87 | QNX IMAGE FILESYSTEM (IFS) V6 | FILESYSTEM | Fully support |
88 | QUALCOMM FBPK V1 | FILESYSTEM | Fully support |
89 | QUALCOMM FBPK V2 | FILESYSTEM | Fully support |
90 | QUALCOMM FBPK V2 | FILESYSTEM | Fully support |
91 | QUALCOMM MIBIB | EXECUTABLE | Fully support |
92 | RAR | ARCHIVE | Encrypted RAR files are not supported |
93 | ROCKCHIP RKAF | FILESYSTEM | Fully support |
94 | ROCKCHIP RKFW | FILESYSTEM | Fully support |
95 | ROCKWELL COB1 | ARCHIVE | Fully support |
96 | ROMFS | FILESYSTEM | Fully support |
97 | SAUTER | ARCHIVE | Fully support |
98 | SMA SOLAR SMA | ARCHIVE | Fully support |
99 | SQUASHFS (V1) | FILESYSTEM | Fully support |
100 | SQUASHFS (V2) | FILESYSTEM | Fully support |
101 | SQUASHFS (V3) | FILESYSTEM | Fully support |
102 | SQUASHFS (V3-BROADCOM) | FILESYSTEM | Fully support |
103 | SQUASHFS (V3-DDWRT) | FILESYSTEM | Fully support |
104 | SQUASHFS (V3-NON-STANDARD) | FILESYSTEM | Fully support |
105 | SQUASHFS (V4-BE) | FILESYSTEM | Fully support |
106 | SQUASHFS (V4-LE) | FILESYSTEM | Fully support |
107 | STUFFIT SIT | ARCHIVE | Fully support |
108 | STUFFIT SIT (V5) | ARCHIVE | Fully support |
109 | TAR (UNIX) | ARCHIVE | Fully support |
110 | TAR (USTAR) | ARCHIVE | Fully support |
111 | UBI | FILESYSTEM | Fully support |
112 | UBIFS | FILESYSTEM | Fully support |
113 | UEFI | ARCHIVE | Currently only supports Flash descriptor extraction |
114 | UIMAGE | ARCHIVE | Fully support |
115 | USB FLASHING FORMAT (UF2) | EXECUTABLE | Fully support |
116 | UZIP | COMPRESSION | Fully support |
117 | VMWARE VIRTUAL MACHINE DISK | FILESYSTEM | Fully support |
118 | VXWORKS MEMFS | FILESYSTEM | Fully support |
119 | WEBROM | ARCHIVE | Fully support |
120 | X86 LINUX KERNEL | EXECUTABLE | Fully support |
121 | XIAOMI HDR1 | ARCHIVE | Fully support |
122 | XIAOMI HDR2 | ARCHIVE | Fully support |
123 | XILINX FSBL | EXECUTABLE | Fully support |
124 | XZ | COMPRESSION | Fully support |
125 | YAFFS | FILESYSTEM | Fully support |
126 | YEALINK ROM | FILESYSTEM | Fully support |
127 | YEALINK SQUASHFS | FILESYSTEM | Fully support |
128 | YEALINK UBI | FILESYSTEM | Fully support |
129 | YEALINK YAFFS | FILESYSTEM | Fully support |
130 | ZIP | ARCHIVE | Encrypted ZIP files are not supported |
131 | ZLIB | COMPRESSION | Fully support |
132 | ZSTD | COMPRESSION | Fully support |
Related






